Security Onion
Security Onion is a comprehensive open-source platform designed for intrusion detection, network security monitoring, and log management. This overview aims to provide a more specialized understanding of its architecture, features, and operational best practices.
Architecture Overview
Security Onion operates on three primary layers:
- Full Packet Capture:
- Utilizes tools like netsniff-ng to capture and record all network traffic. This capability is crucial for forensic analysis and incident response, allowing security teams to review past network activities.
- Intrusion Detection Systems (IDS):
- Network-Based IDS (NIDS): Implements both Snort and Suricata, which use rules-driven methods to identify malicious traffic patterns. They analyze packets against known signatures to detect anomalies.
- Host-Based IDS (HIDS): Incorporates Wazuh, which is installed on endpoints to perform log analysis, file integrity checks, and real-time alerts. This dual approach enhances security by monitoring both network and host activities.
- Zeek (formerly Bro): Provides high-level network analysis, logging various aspects such as DNS requests and SSL certificates. It also checks files against malware registries.
- Analysis Tools:
- Tools like Sguil and Squert aggregate data from different sources, providing context for alerts and facilitating collaborative investigations. The Elastic Stack (Elasticsearch, Logstash, Kibana) is integrated for log management and visualization.
Key Features
- Comprehensive Monitoring: Security Onion offers both network visibility through packet capture and host visibility via the Elastic Agent, allowing for detailed monitoring of all digital assets.
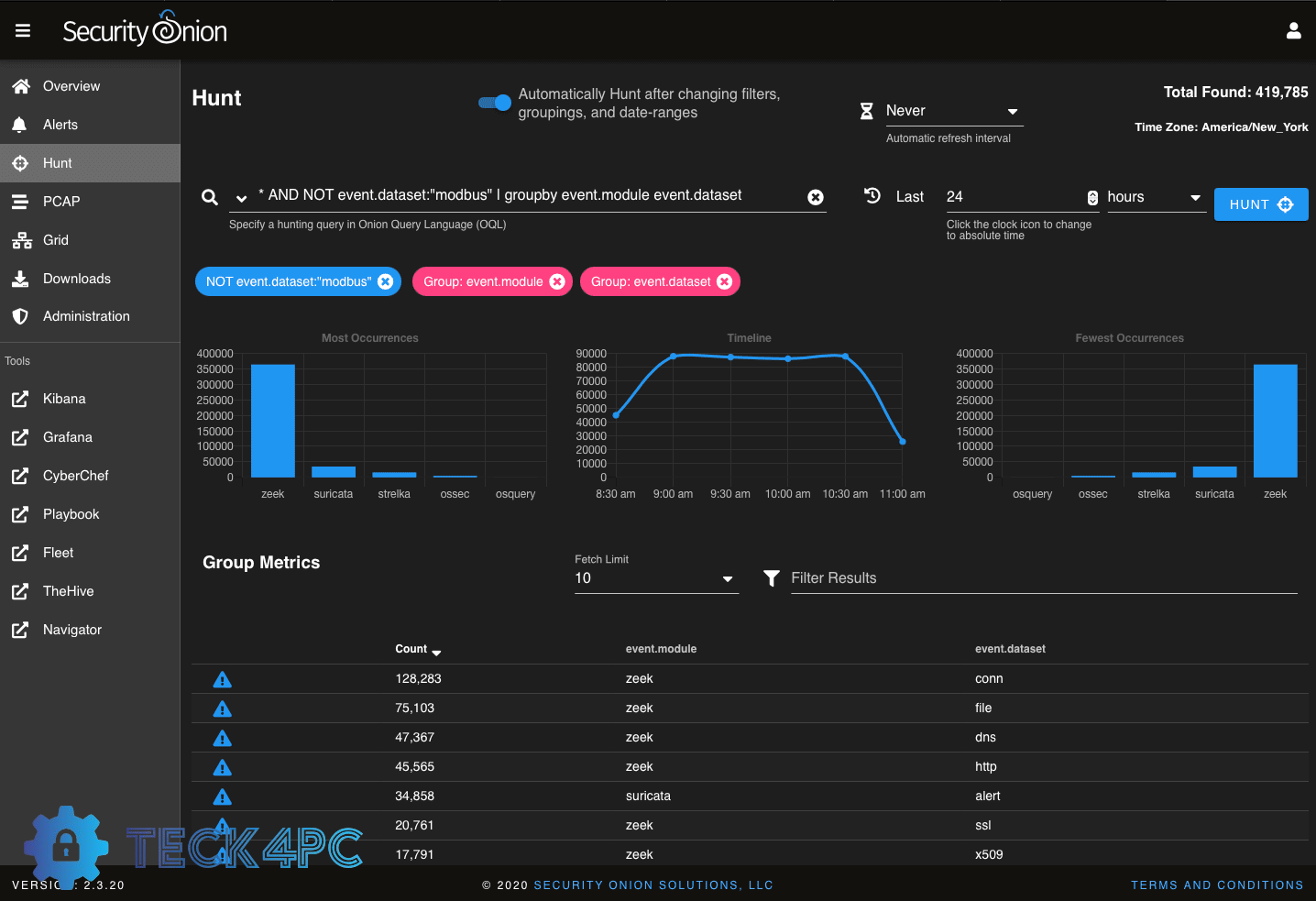
- Threat Hunting Capabilities: Users can conduct proactive threat hunting using pre-built dashboards or custom queries in Kibana.
- Case Management: Facilitates tracking of incidents from detection through resolution, ensuring that security teams can manage their responses effectively.
- Scalability: The platform supports flexible deployments, whether on a single machine or distributed across multiple nodes.
Recent Updates
The latest version, Security Onion 2.4.x, introduced several enhancements:
- Unified Elastic Agent: Replaced multiple agents with a single Elastic Agent for streamlined endpoint monitoring and management.
- Improved User Interface: Administrative tasks can now be performed directly through the web interface, reducing the need for command-line interactions.
- New Detections Feature: Simplifies the process of tuning detection rules and creating new ones, enhancing usability for analysts.
Operational Best Practices
- Regular Updates:
- Keep Security Onion updated to leverage new features and security patches. Regular maintenance ensures optimal performance.
- Resource Management:
- Allocate sufficient resources based on your deployment size. Larger networks may require dedicated hardware or additional nodes to handle increased traffic.
- Integration with Other Tools:
- Consider integrating Security Onion with other security solutions such as SIEMs for a more holistic view of your security landscape.
- Training and Documentation:
- Utilize the extensive documentation available online to familiarize yourself with the platform’s capabilities. Engage with community forums for shared knowledge and best practices.
- Testing New Features:
- Before deploying new features in a production environment, test them in a controlled setting to understand their impact on your existing infrastructure.
System Requirements for Security Onion Installation
If you’re considering installing Security Onion for enhanced network security and monitoring, it’s essential to ensure your system meets the necessary requirements. Below are the recommended specifications to achieve optimal performance:
Minimum System Requirements
- CPU: A multicore CPU with at least 2 cores (4+ cores recommended for better performance)
- RAM: Minimum of 16GB (32GB recommended)
- Disk Space: At least 200GB of available storage
- Network: A bridged network configuration is recommended for seamless connectivity
Download Link
Ready to get started? You can download the latest version of Security Onion from the official website: Download Security Onion.
Conclusion
Security Onion serves as a robust framework for organizations aiming to enhance their cybersecurity posture through effective monitoring and incident response capabilities. By leveraging its multi-layered architecture and advanced features, security teams can gain deeper insights into their network activities and respond promptly to potential threats.

